Today businesses are more inclined towards moving their workloads to Cloud to cut capital investments and maximize operational efficiency. Hosting the workloads to the AWS cloud is one part, and ensuring the application’s security is another that must be taken seriously. When it comes to Cloud, there is always a misunderstanding that the security will be handled by default when you move the workloads to Cloud. But this is not the case; security in Cloud is a shared responsibility, and the customer must ensure that preventive measures are in place to protect from ongoing threats. However, several services are available from AWS to ensure your web application is protected. This is where AWS WAF comes into the picture.
What is AWS WAF?
AWS WAF, or Web Application Firewall, acts as a barrier between your workloads and the internet protecting the web applications from common cyber attacks such as SQL injection or cross-site scripting. It also lets you configure rules that allow, block, or monitor web requests based on the conditions you define, like IP address filtering, HTTP headers etc.
How does AWS WAF Work?
Instead of provisioning separate servers for managing the firewall, AWS WAF lets you integrate with the supported services. It works by inspecting the incoming traffic w.r.t the preconfigured rule sets. When an underlying service receives a request for your web application, it will get redirected to WAF, which checks the demand to see if it complies with the preconfigured rule set. If it meets the required condition, WAF will let the underlying service accept the request; otherwise, it will get blocked, as shown in the figure below.
How to deploy AWS WAF?
AWS WAF can currently be deployed along with the following services,
1. Amazon CloudFront:
- When deployed along with CloudFront, it will be part of the CDN network protecting the contents at the origin. It also ensures the protection of the resources cached at the edge locations.
2. Application Load Balancer (ALB):
- It will protect the instances running behind the load balancer when deployed along with ALB.
3. Amazon API Gateway:
- When deployed along with API Gateway, it will protect the REST APIs from web exploits.
How to set up AWS WAF?
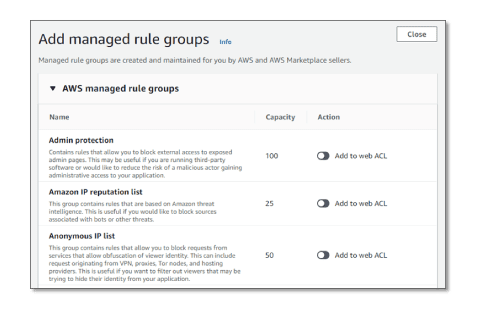
To start with AWS WAF, we must create a web Access Control List (ACL) and associate it with the supported services. ACLs should contain at least one rule or multiple rules that we specify to either block or allow incoming requests. There is flexibility to write your own rule sets or use managed rule groups offered by AWS and AWS Marketplace sellers. Some of the AWS-managed rules are shown in the figure below.
You can also set up Rate-based Rules that block a specific IP address/range that requests more than the specified count for a given time. E.g. We can block an IP address asking more than 1000 times within a 2-minute interval.
Both Rate-based and regular rules can be added as part of the same rules set to add more flexibility to the user.
How is WAF priced?
Like the other services, AWS WAF has a pay-as-you-go pricing model with no upfront commitments. There are different costing components for AWS WAF, as mentioned below,
- $5/Month for each web ACL created
- $1/Month for each rule that is added to the web ACL
- $0.60/Month per million requests that WAF processes.
There are no additional charges for using AWS Managed Rules or Rate-based rules, but if you use third-party Managed Rules from the Market Place, additional costs will be applied as described by the seller.
To summarize, organizations need to ensure perimeter-level security when they move their workloads into Cloud. Tightly integrated with other AWS services, AWS WAF is a no-brainer in setup and has a very straightforward pricing model, making it an easy choice for protecting your workloads on the AWS cloud.




