Cloud security has evolved from a technical concern into a strategic business priority in 2026. As enterprises migrate sensitive workloads, customer data, and intellectual property to the cloud, the attack surface has expanded dramatically. Industry reports consistently highlight that most cloud security incidents are caused by misconfigurations, excessive permissions, and lack of governance – not flaws in cloud platforms themselves.
Do You Know? 23% of cloud security incidents are caused by misconfigurations.
AWS supports millions of workloads globally, including some of the most regulated and high-risk environments. From Rapyder’s real-world experience working with enterprises across healthcare, fintech, SaaS, and public sector domains, one insight stands out clearly: strong AWS cloud security is less about tools and more about architecture, governance, and discipline.
This guide explains what AWS cloud security is, why it matters, the principles it is built on, and how organizations can secure AWS environments using proven best practices, checklists, and tools in 2026.
What Is AWS Cloud Security?
AWS cloud security refers to the combination of services, controls, processes, and best practices used to protect applications, data, and infrastructure running on Amazon Web Services.
From a business-first perspective, AWS cloud security ensures:
- Business continuity
- Customer trust
- Regulatory compliance
- Protection against financial and reputational loss
AWS provides a highly secure infrastructure by default, but security operates under a shared responsibility model. While AWS secures the physical data centers and underlying infrastructure, customers are responsible for securing identities, data, workloads, network configurations, and application logic. This shared approach offers flexibility; but also demands accountability.
Why AWS Cloud Security Matters for Modern Enterprises
Protection of Sensitive Data
Cloud environments host customer data, financial records, and intellectual property. Strong security prevents data breaches and unauthorized access.
Regulatory and Compliance Readiness
Industries governed by HIPAA, PCI DSS, ISO, SOC 2, and GDPR depend on AWS security controls to meet audit requirements.
Business Continuity and Availability
Security incidents often cause downtime. A secure AWS environment ensures availability even during attacks or failures.
Faster, Safer Innovation
Security enables organizations to move fast without introducing unacceptable risk.
Long-Term Brand Trust
Security failures directly impact customer confidence and retention.
Common Challenges and How to Overcome Them
Misconfigured Permissions
Overly permissive IAM roles remain one of the most common causes of breaches.
How to overcome: Implement least privilege access, role-based permissions, and regular access reviews.
Lack of Visibility Across Multi-Account Environments
As organizations scale, security visibility becomes fragmented.
How to overcome: Centralize logging using AWS CloudTrail, AWS Config, and Security Hub.
Security Cost Management
Security tools can appear expensive if not planned properly.
How to overcome: Enable services selectively and automate alerting instead of over-provisioning.
Skill Gaps
AWS security requires specialized expertise.
How to overcome: Upskill teams through AWS Security – Specialty certification and hands-on training.
Role of AWS Security Services
AWS offers native services that form the backbone of cloud security:
- AWS IAM – Controls who can access what
- AWS GuardDuty – Continuously detects threats using ML
- AWS Security Hub – Aggregates and prioritizes findings
- AWS WAF & Shield – Protect against web exploits and DDoS
- AWS Macie – Identifies and protects sensitive data
Together, these AWS services enable proactive threat detection and governance.
Core AWS Cloud Security Principles
Shared Responsibility Model
Security responsibilities are divided between AWS and customers. Understanding where AWS responsibility ends, and yours begins, is foundational to avoiding gaps.
Zero-Trust Access
No user, workload, or service is trusted by default. Every request is authenticated, authorized, and logged, reducing lateral movement risks.
Defense-in-Depth
AWS cloud security relies on layered controls; identity, network, application, and data, so that if one layer fails, others still protect the system.
Continuous Monitoring & Automation
Security is ongoing, not reactive. Automated detection, alerting, and remediation reduce response time and human error.
Encryption Everywhere
All sensitive data must be encrypted at rest and in transit using AWS KMS and TLS to prevent exposure even if access controls fail.
Compliance & Governance Built-In
Policies, guardrails, and audits are automated to ensure consistent security across environments.
These AWS cloud security principles are essential for building resilient architectures at scale.
Advantages of AWS Cloud Security
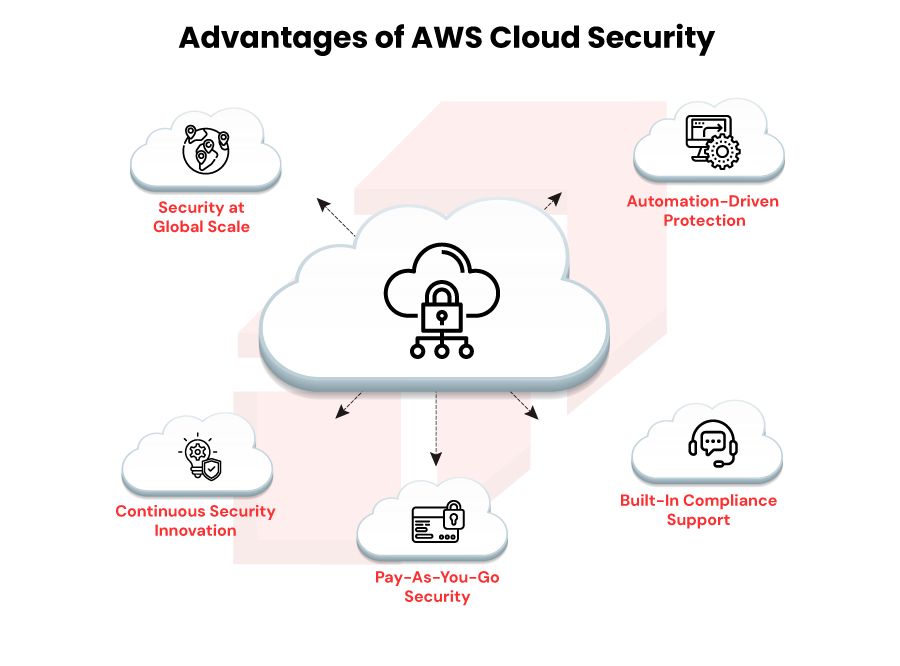
Security at Global Scale
AWS secures infrastructure across regions and availability zones, something difficult to replicate on-premises.
Continuous Security Innovation
AWS regularly releases new security features, keeping customers protected against evolving threats.
Pay-As-You-Go Security
Organizations pay only for the security services they use, avoiding large upfront investments.
Built-In Compliance Support
AWS aligns with global compliance frameworks, simplifying audits and certifications.
Automation-Driven Protection
Automation reduces manual effort, configuration drift, and operational risk.
AWS Cloud Security Checklist
Identity & Access
- Enforce MFA
- Apply least privilege
- Rotate credentials regularly
Data Protection
- Encrypt all data
- Secure backups
- Classify sensitive data
Network Security
- Isolate workloads using VPCs
- Restrict inbound traffic
- Use WAF rules
Monitoring & Incident Response
- Enable CloudTrail and GuardDuty
- Centralize logs
- Test incident response plans
Compliance
- Run regular audits
- Automate policy enforcement
This AWS cloud security checklist helps organizations stay audit-ready.
AWS Cloud Security Best Practices (2026)
1.Strengthen Identity & Access Management
IAM remains the primary attack vector. Use short-lived credentials, role-based access, and zero trust models.
2.Enable Encryption & Data Resilience
Encrypt everything and automate backup strategies to ensure data availability and recovery.
3.Secure Network & Perimeter Controls
Adopt private networking, VPC segmentation, and restricted ingress points.
4.Shift-Left Security with DevSecOps
Integrate security checks early in CI/CD pipelines to catch issues before deployment.
5.Implement Continuous Monitoring
Use real-time threat detection and automated remediation to reduce response times.
6.Governance, Risk & Compliance
Continuously enforce policies, monitor risk posture, and generate audit evidence.
Tools to Implement AWS Cloud Security
AWS Native Tools
- IAM
- GuardDuty
- Security Hub
- Macie
- WAF
Third-Party Tools
- SIEM platforms
- CSPM solutions
- Vulnerability scanners
Each tool plays a role in a layered security approach.
Real-World Examples & Case Studies
In one AWS cloud security engagement, Rapyder partnered with a rapidly scaling digital platform where growth had outpaced security controls. Multiple AWS accounts, teams, and services had led to uncontrolled identity growth, inconsistent access policies, and limited end-to-end visibility – increasing both security risk and audit pressure.
Rapyder redesigned the IAM framework from the ground up, enforcing least-privilege access, standardizing role definitions, and centralizing security monitoring across accounts. Automated guardrails and continuous visibility helped the organization quickly identify and remediate risks as the environment evolved.
As a result, the platform saw a significant reduction in security findings, faster audit cycles, and improved confidence among internal stakeholders – proving how structured governance and automation can turn cloud security into an enabler, not a blocker.
Expert Insight from Rapyder
“Strong AWS security isn’t about deploying more tools – it’s about consistent governance, visibility, and automation across every account.”
— Cloud Security Architect, Rapyder
How Rapyder Helps Secure AWS Environments
Rapyder helps enterprises design, implement, and operate AWS environments where security is built into the foundation – not added as an afterthought. We work closely with businesses to align cloud security with actual risk exposure, regulatory requirements, and long-term growth goals.
With deep experience across regulated industries, we go beyond checkbox compliance. Our approach focuses on creating scalable security architectures, implementing the right guardrails, and continuously strengthening posture as workloads evolve. From identity and access controls to threat detection, governance, and operational security, we ensure protection keeps pace with scale.
The outcome is an AWS environment that stays resilient, compliant, and adaptable – so teams can move fast without compromising on security.
If your cloud is growing faster than your security, it’s time to fix that – before risk catches up. Click here to know how Rapyder team secure you cloud infrastructure. Let’s build AWS security that scales with your business.
Conclusion
AWS cloud security in 2026 is a continuous discipline that combines technology, governance, and culture. By understanding what AWS cloud security is, applying proven principles, and following structured best practices, organizations can protect their environments without slowing innovation.
Enterprises that treat security as an enabler, not a blocker, are best positioned to grow securely on AWS.





